I had been watching Twitter all day yesterday and amongst all the #infosecbikini photos filling up InfoSec Twitter there was mention of this critical Windows vulnerability. At first it sounded like the June patches would protect you, then Twitter seemed to lose faith that was the case.
The US Cybersecurity & Infrastructure Security Agency (CISA) released the following notice the evening of June 30, 2021. (https://us-cert.cisa.gov/ncas/current-activity/2021/06/30/printnightmare-critical-windows-print-spooler-vulnerability)
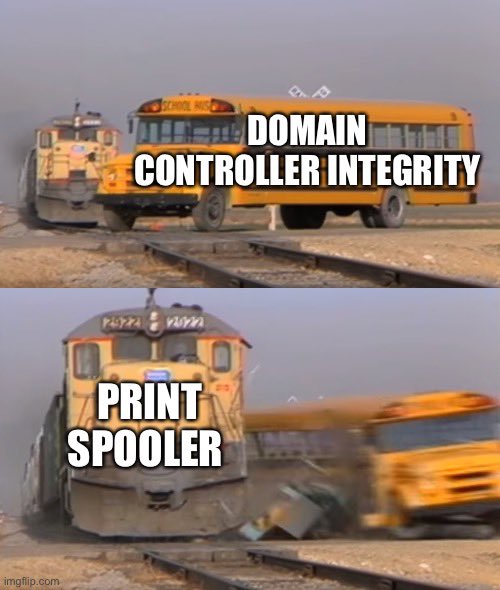
It has been recommended to disable the Windows Print spooler service on Domain Controllers and any systems that do not print.
EDIT: As of writing this entry the best workaround I have been able to find if you need to keep print services running is here: https://blog.truesec.com/2021/06/30/fix-for-printnightmare-cve-2021-1675-exploit-to-keep-your-print-servers-running-while-a-patch-is-not-available/
EDIT 2: Microsoft has finally responded: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-34527
EDIT 3: CISA put out emergency directive: https://cyber.dhs.gov/ed/21-04/
For your meme viewing pleasure: